
Importance
The increasingly stringent global personal data protection laws and regulations on Artificial Intelligence (AI), together with more cyber threats, pose significant challenges to OR’s business operations in the digital era. These impacts are directly related to the management of customer and user data. Without robust safeguards, such risks may lead to business damage, violations of privacy rights, and a loss of confidence among stakeholders. Therefore, enhancing data security and privacy measures can also generate positive impacts by strengthening trust in OR, supporting personal data protection, and enhancing long-term business competitiveness.
OR is committed to leveraging digital technologies and AI in business operations to enhance operational efficiency and respond to the consumers and customers in a timely manner. It also is aware of the risks of business operations that might be related to data security and privacy, such as malware phishing, which is classified as one of the cyber threats that may cause damages to both the business operations and the company’s reputation. Therefore, effective management of data security and privacy is required to meet the expectations of the customer, and to deliver value to all stakeholder groups through quality and safe products and services.
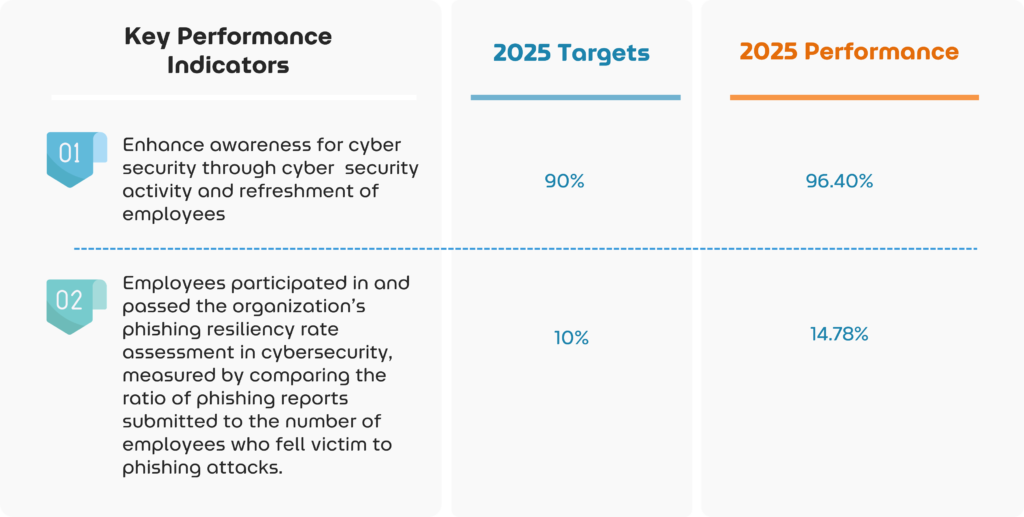
2025 Targets
Management Approach
Data Security and Privacy Policy
OR emphasizes and focuses on managing work in accordance with the Personal Data Protection Act. B.E. 2562 (2019) (PDPA) and secondary laws issued under the Act. Therefore, it has created the Data Privacy Policy of the Company, which includes the Company’s internal structure, policies, and practices related to personal data protection. It applies to all operations of the Company including employees, operators, customers, suppliers, contractors, agents, representatives, directors, executives, as well as other types of personnel of the Company.
OR therefore issues privacy notices and policies, categorized according to the utilization of stakeholder groups into the following 4 groups:
1. Business Partner Privacy Notice
2. Customer Privacy Notice
3. Human Resources Privacy Notice
4. Internal Privacy Policy, which consists of various sub-policies relating to the entire operations within the OR
For all these privacy notices and policies, OR meticulously plans and designs the privacy notice and policy notification process, ensuring that appropriate consent is obtained for each stakeholder group.
[Learn more about privacy notices and policies for OR’s business partners and customers click: https://pdpa.pttor.com/]
Through these comprehensive privacy notices and policies, OR demonstrates its commitment to safeguarding personal data, covering both internal and external privacy perspectives, including businesses owned or operated by OR, suppliers, and customers across various businesses. This aims to create security and the privacy of personal information and ensures that the OR collects, uses, and discloses information appropriately, in a way that meets the purpose stated to the personal data owner.
In addition, OR also sets the Information Policy. It is a policy on confidentiality, data retention, and usage of inside information. It also sets the OR Enterprise Data Governance policy to establish management directions and support safe information and communications that align with business needs and comply with relevant laws and regulations for all employees. This includes a Digital Standards manual for OR.
OR has also created additional policies and processes, such as the Consent Management process, Data Retention Standard, Incident Response Procedure for personal data breach, Data Security Incident Reporting and Response Policy, Record of Processing Activities, and Guidance on Data Protection Officer Representative, etc.
Data Security and Privacy Governance
The governance structure follows the Three Lines Model to facilitate control, oversight, and auditing, with clear segregation of duties. This is carried out by the Enterprise Risk Management Committee (ERMC), which oversees cyber security and information technology strategies. OR has appointed the OR Digital & Data Governance Steering Committee (DGSC), chaired by the Executive Vice President of Corporate Strategy and Sustainability, with the Executive Vice President of Digital Business and Solutions as the vice-chair. The Chief Information Security Officer (CISO) is responsible for overseeing the implementation of information technology and digital operations, ensuring alignment with OR’s policies, directions, and business strategies, as well as those of the OR Group companies.
Data Security and Data Privacy Governance Structure
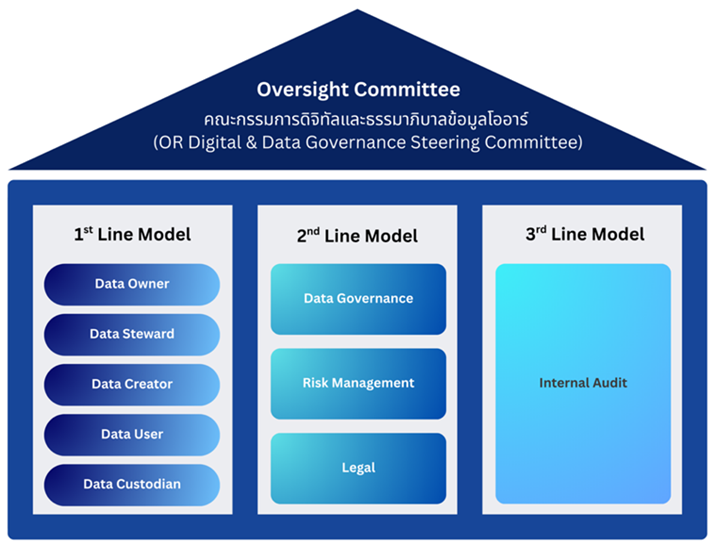
| Level | Committee/Department | Responsibility |
|---|---|---|
| Board Level | Enterprise Risk Management Committee |
|
| Operational Level | 1st Line Model (Process Owners) | Support data management in accordance with OR’s data governance policies, standards, and practices.
|
| 2nd Line Model | Responsible for oversight and establishing data governance frameworks:
| |
| 3rd Line Model | Internal Audit
|
OR has established clear reporting procedures that employees can follow when suspicious observations arise. OR has designated responsible individuals and functions to act as Points of Contact for matters related to data security, privacy, and cybersecurity. Clear notification and incident‑reporting procedures are communicated to all employees, enabling them to promptly report any incidents that pose risks to the responsible departments without delay. The responsible units are required to escalate such incidents to the Company’s executives or relevant stakeholders and to analyze and manage the risks to an acceptable level in accordance with OR’s enterprise risk management framework.
In 2025, OR conducted an Internal Audit to review compliance with the Company’s Privacy Policy, ensuring alignment with applicable policies, standards, and procedures related to data governance. The audit was performed on a sampling basis, focusing on groups of personal data owners and activities involving large‑volume personal data processing.
Data security, data privacy, and cybersecurity form part of employee performance assessments and disciplinary actions. OR evaluates employee performance in cybersecurity through phishing‑email tests conducted for all employees to ensure compliance with Company policies. All OR personnel are required to comply with the Company’s Information Technology Security Requirements, the Information Technology Security Management Policy, and the Cybersecurity Policy.
In addition, OR provides training for new employees to ensure their understanding of the policies, rules, regulations, requirements, practices, and standards related to the Company’s data security. The training also includes awareness of laws related to the Computer Crime Act, cyber threats such as malware and phishing, associated penalties, and the consequences of misuse or improper use of information systems.
Further information is available in the 2025 OR Group Way of Conduct and Corporate Governance, Ethical Standards and Code of Business Ethics Handbook
Risk Assessment and Identification
OR specifies the Key Risk Indicator (KRI) on the topic of IT Infrastructure Instability and Cybersecurity. This is for systematic performance monitoring and ensuring that the business has a surveillance and that it monitors risks that may arise from data security and privacy issues.
Records of Processing Activities are maintained by all departments as a database of each department and the organization that are involved in personal data. This facilitates easy tracking and verification to ensure compliance with the intended purposes of data usage and alignment with relevant legal frameworks. The Records of Processing Activities are conducted according to the requirements of the Personal Data Protection Act, B.E. 2562 (2019).
Data Security, Privacy, and Cybersecurity
Committed to conducting business under the concept of Digital Driven Organization, OR is prepared for risks arising from security, data privacy, and cyber threats. OR complies with ISO/IEC 27001:2022 standards and the cyber security framework developed by National Institute of Standards and Technology (NIST). The framework covers the entire spectrum from information asset identification, risk assessment, and governance through asset management systems (e.g., IT Asset Management) and risk assessment systems (Identify: ID.AM, ID.RA, ID.GV). Protective measures include access control mechanisms such as Identity Providers (IDP) for authentication and authorization, the use of Two-Factor Authentication, data encryption (e.g., AES-256, TLS 1.2/1.3), data classification tools, Data Loss Prevention (DLP) systems, as well as firewalls, perimeter protection, and malware protection systems (Antivirus, EDR) (Protect: PR.AC, PR.DS, PR.PT). Detection of incidents is enabled through monitoring and log management systems (SIEM) to identify abnormal behavior and real-time threats (Detect: DE.CM, DE.AE). Incident response is carried out through an Incident Response Plan, incident management systems (ITSM), investigation and containment procedures using EDR, and communication with relevant stakeholders (Respond: RS.RP, RS.MI, RS.CO).
In addition, system recovery is supported by recovery and backup plans (Backup Tools) and post-incident reviews to improve processes (Recover: RC.RP, RC.IM), enabling OR to deliver continuous and secure services in accordance with international standards.
OR’s customer security and privacy has a clear policy. This is in line with the Personal Data Protection Act (PDPA). OR sets cookies to store or track information about the use of websites, and to analyze the Trend. Website management will track the website visit of the user to remember the user’s preferences. In this regard, the OR has a tracking record of customer data usage, in accordance with the announced customer privacy policy.
To ensure that OR’s information systems are safe, OR conducts security testing and engages external specialists to test its information‑security systems through third‑party vulnerability analysis, including Penetration Testing. OR has also developed a Disaster Recovery Plan to provide clear guidance to executives and relevant personnel regarding their roles, duties, and operational procedures in the event of a data‑security or privacy incident. As part of Information Security within Business Continuity Management, OR performs reviews of its established security‑continuity measures at least twice per year.
Audits for compliance with the OR’s personal data security policy and cybersecurity are done by internal auditors as well as third-party audit annually. This is in accordance with the ISO/IEC 27001:2022. The results of operations related to data security and privacy, as well as cybersecurity is recorded and analyzed for the possibility of improving the security and data privacy management system, as well as specifying a plan for future business operations
Overall of internal audit conducted in 2025 for personal data protection operations is complied with principles and requirements of the Personal Data Protection Act B.E. 2562 (2019), sub-regulations (notifications), and other relevant announcements. The inspection is categorized into two aspects: legal preparation and personnel and organization’s procedure preparation. The main topics are as follows:
- Obtaining consent
- Processing of personal data (Collection, Use, Disclosure of Personal Data)
- Notification of details and objectives to the data subject
- Baseline used for data processing
- Sending or transferring data abroad
- Data Subject Rights
- Duties of the data controller
- Recording of personal data processing activities
- Duties of data processors / contracts for processing personal data
From the audit, it was found that OR has prepared itself so that the organization, personnel, and related processes can conduct business appropriately in accordance with legal requirements. OR has an annual internal audit plan to ensure that the organization can conduct business in accordance with the aforementioned relevant laws.
Complaint Channel
OR provides complaint channels for reporting personal data breaches, accessible via the 1365 Contact Center or through email at dpo@pttor.com. All such complaints are reported to the Data Protection Officer (DPO) and acknowledged by the relevant departments. The information is then analyzed, and appropriate corrective and remedial actions are planned in accordance with the Incident Response Procedure.
In the event that OR discovers a leak of personal information, OR must report the data breaches, as stipulated in the Personal Data Protection, B.E. 2562 (2019). This includes violations that have a high risk of affecting the rights and freedoms of the individual. The remedy guidelines must also be informed without delay and must be notified to the office of the Personal Data Protection Commission.
Performance
In 2025, OR identified one data leakage incident involving general business‑partner data, which did not affect any personal data owners. The incident was immediately contained, and additional security measures were implemented to prevent recurrence.
Upon detecting or being notified of a potential personal data breach, the responsible departments promptly assess the situation and contain the incident — including suspending user accounts, resetting passwords, and disabling system access before investigating the cause and determining the scope of affected data. A report is then prepared and submitted to the Data Protection Officer (DPO) for onward notification to the Office of the Personal Data Protection Commission (PDPC) within the legally required timeframe.
Affected data subjects are also notified without delay, along with appropriate remedy guidelines. Permanent system‑control improvements, such as the implementation of Multi‑Factor Authentication (MFA) and post‑incident reviews, are carried out to prevent recurrence.
In 2025, OR received no complaints regarding customer privacy violations or customer data loss for secondary purposes
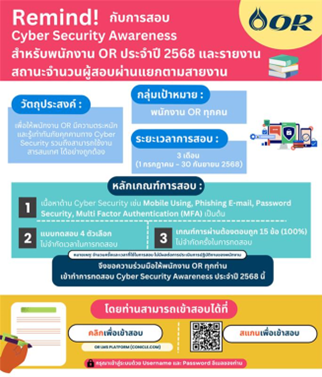
1. Cyber Security Awareness Training with Test for OR’s Employees
The E-learning training is designed to help employees understand digital service delivery, policies, regulations, practices, and standards related to the company’s information security. This also includes the understanding of laws related to the Computer-related Crime Act, threats, and consequences of misuse and improper use of information systems. Training content includes Password Security, Phishing Emails, Malware Protection, and Internet Using Security, presented through animation for improved engagement. A Refreshment Course (Cyber Security Awareness Exam) is administered to long‑serving employees. In 2025, 98.55% of participants passed the test.Contractor personnel working for OR are also required to take the Cyber Security Awareness test, with 100% passing in 2025.
2. Personal Data Protection Training for Employees
In 2025, the training on personal data protection for employees includes the Personal Data Protection Act B.E. 2562 (2019) (PDPA) in online format. This course is designed for employees from departments responsible for handling customer personal data. The objective is to ensure employees understand an appropriate collection and management of personal data in compliance with the Personal Data Protection Act, B.E. 2562 (2019), and to follow appropriate procedures in the event of a personal data breach.
3. Prevention of AI-Driven Spear Phishing Threats
OR enhances cybersecurity awareness by disseminating guidelines for preventing AI-driven spear phishing through employee education. This includes training personnel to scrutinize emails, observe the “External” warning indicator, and report suspicious incidents via the 24‑hour Service Desk. OR also actively campaigns against clicking suspicious links or opening suspicious attachments. These actions help strengthen proactive vigilance capabilities and reduce risks from threats to OR’s information systems.

4. AI Governance Training: Governance of Artificial Intelligence Usage
AI Governance training, focusing on the governance of Artificial Intelligence usage, or AI governance, was conducted in 2025 as an online E-learning course via the OR LMS platform. The training comprised three core modules: 1) What is AI, 2) AI Risk, and 3) AI Governance. The objective of the program was to build employees’ foundational understanding of AI, together with key concepts, associated risks, and practical guidelines that OR can apply to appropriately and safely govern the development and use of AI.

Related Documents
Site map
- About
- Organization
- Career
- Oil Business
- - Retail Energy Solution
- - Commercial Business
- Retail Business
- Services
- International Business
- Business Opportunity
- Sustainability
PTT Oil and Retail Business Public Company Limited
555/2 Energy Complex Building B, 12th Floor, Vibhavadi Rangsit Rd., Chatuchak, Bangkok 10900
© 2024 OR Tel : 02 196 5959


